When you mention security to a site owner, their first thought normally won’t be of their social media profile data. It’s more often the thought of site security – protection against hacking, malware, even spam. Expanding the conversation a little, the dangers of clicking on links and downloading files is bound to come up. A step further might bring up SSL issues on login pages.
But many netizens neglect their point of greatest vulnerability – that of their profiles – on social media platforms, forums, blogs, etc. Everywhere you have any personal information about you, is a potential threat, because with the social graph as it is today, much of that information can be easily aggregated to form a complete picture of you.
Hacking, identity theft, character assassination, theft of funds or spamming… there are entire industries out there focused on accumulating such information to accomplish one or more of those.
Whose Responsibility is your Security?
There was an interesting conversation in the SEO Dojo, stemming from an article on Search Engine Watch. Miranda Miller’s article discussed a blogger’s purchase of a list of one million Facebook usernames, account numbers and emails, for the princely sum of $5 USD. I think it’s safe to say that any social media user should be concerned that such a thing could happen, at any price.
The discussion in the Dojo took a slightly different turn, though. We were discussing the ethical nature of such a thing being possible (enabled?) and where the responsibility lies to prevent it. Let’s take a look at the second question… whose responsibility is it to protect a user’s privacy?
Sidestepping the legal aspect and focusing on purely the responsibility, it seems to me that such a question is rhetorical. If I’m concerned with my personal online security, then I believe that ultimately, the responsibility rests on my shoulders to ensure that I take all possible measures to safeguard my personal data.
Obviously, you need to make a judgment call regarding how much information you choose to share with any site, application or other user. That means you need to read and understand the TOS (Terms of Service) and Privacy Statement for any site, before you disclose any of your information to them. It also means that you need to decide how much confidence you have that they will live up to those terms.
Those two items should be fairly obvious. But there are other aspects to be considered, too. For instance:
[list type=”bullet3″]
- How secure is that data? We’ve all seen reports of hackers having successfully invaded the database of prominent online businesses to harvest emails and credit card data. Good intentions, coupled with poor security, can still spell disaster, if you’re one of the unfortunate people on that list of stolen profiles.
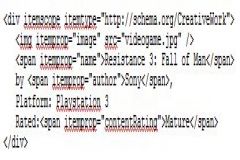
- Who has normal access to that data? Now we’re getting to the heart of our conversation! Applications and APIs that make use of a platform’s database presumably acquire such access by pledging to use that data only within certain limits. Can you trust all of them, too?
[/list]
As it turns out, that last one is full of more holes than a round of Swiss cheese. In Facebook’s Data Use Policy, they explain how your information will be gathered and used, saying:
” We only provide data to our advertising partners or customers after we have removed your name or any other personally identifying information from it, or have combined it with other people’s data in a way that it is no longer associated with you.”
Ah, then there should be no way for a list including name, account and email to be shared with anyone outside of Facebook, right? Well, a person might think that. But while Facebook’s Graph API makes available only the information that you have allowed to be made public, applications (originating outside Facebook) can apparently harvest quite a lot more.
It would appear that that may be how the above-mentioned list of a million users was acquired.
Unfortunately, application developers seem to enjoy fairly unfettered access to a lot more account information than most users think. In order to gain that status, they have to cross their hearts and promise to never use it in any way not allowed. Yeah, THAT’S going to work out real well… just give anybody that can fill out an application the keys to the liquor cabinet, on the honor system.
Where Does the Buck Stop?
The point was made in our discussion that most users don’t really read the TOS before authorizing an application. That may be true. But the question was also asked, Whose fault is that? That is a very valid question, that for me, has only one answer – the user.
My suggestion would be, stop thinking in terms of liability and litigation… Facebook, Twitter, Google+ and just about any other known social media platform has more lawyers and deeper pockets than you do. Think proactively, use some common sense and protect your information.
Don’t assume that if something is potentially dangerous, it would be opt-in. In the case of Facebook, that’s almost never the case. Their default settings are typically those that will provide them the greatest access to your information. They may be the worst, in that regard. But they certainly aren’t the only platform that works that way.
And most importantly, shift your way of thinking – realize that you are NOT a user – you are the product!